How to configure the VPN profile uploaded to AnyConnect using KSP
Last updated July 26th, 2023
Categories:
Environment
- Knox Manage (KM)
- Android Enterprise (AE)
- Knox Service Plugin (KSP)
Overview
The following description is a guide on how to configure the VPN profile uploaded to the AnyConnect application using KSP.
The description describes the detailed steps in the points:
- Adding Cisco AnyConnect application
- Configuration of VPN profile in KSP
Adding Cisco AnyConnect application
Add AnyConnect apps to the managed apps within the Manage Google Play Store in Knox Manage.
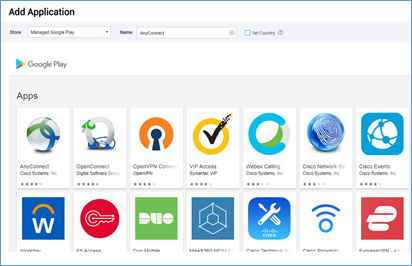
More information on how to add, manage and assign applications can be found here.
Configuration of VPN profile in KSP
- Go to Profiles menu > Samsung Knox > Knox Service Plugin
In Knox Service Plugin, depending on the activation mode of Android Enterprise, select either Device-wide policies*, or Work profile policies.
Does not work in personal space for Android 11 devices using Work Profile On Company-Owned mode.
Follow the steps below to configure the VPN profile for Device Owner mode:
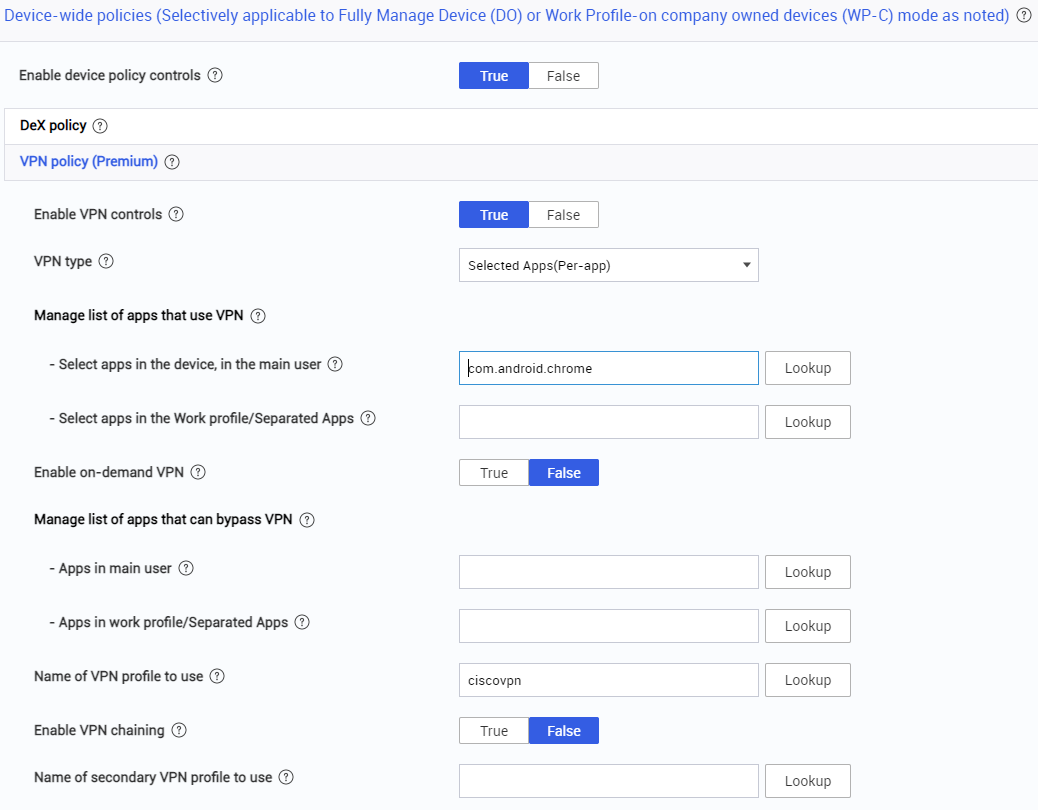
- Go to Device-wide policies > Enable Device policy controls change False button to True button
- Go to VPN (Premium) > Enable VPN controls change False button to True button. You choose Selected Apps (Per-app)
- Go to Manage list of apps that use VPN > Select apps in the main user enter the packed name web browser application. This example uses Chrome Browser: com.android.chrome
- Go to Name of VPN profile to use and enter the name of the profile that you will create later in the configuration. In this example it is ciscovpn
There is a similar configuration for the Work profile, in which case you must first select a policy for the settings Work profile policies (Profile Owner).
The following steps are a continuation of the VPN configuration for a particular VPN vendor.
- Go for VPN profiles (Premium)
- Go to Profile name - enter the profile name from the basic VPN setting. In the example, this is ciscovpn
- Vendor - select Cisco Any Connect
- Host - enter the address of the ASA Cisco serve
- VPN connection type - select SSL or IPsec. In the example, the connection is of SSL type.
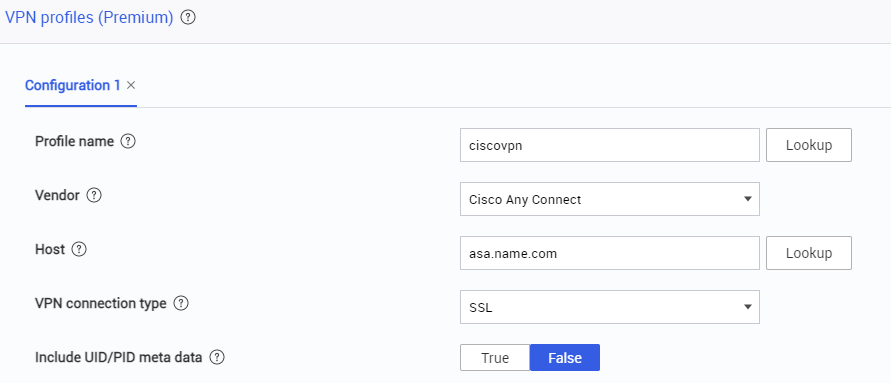
In this example, you do not use the Proxy configuration and leave the option as False. The last setting is the configuration for the AnyConnect client by connection type.
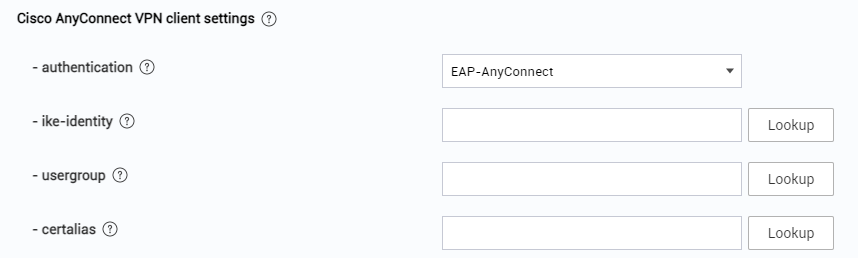
- Go to authentication - For SSL connection type, select EAP-AnyConnect
Depending on the configuration of the Cisco ASA, the others should be filled in according to the requirements of your company’s VPN connection configuration. In the example configuration, the fields are blank.
On this page
Is this page helpful?